Integrates Sec1 Security scanning into your CI/CD pipeline, enabling teams to identify vulnerabilities and security issues early in the development lifecycle.
To use the plugin up you will need to take the following steps in order:
- Install the Sec1 Security Plugin
- Configure a Sec1 API Token Credential
- Add Sec1 Security to your Project
- Go to "Manage Jenkins" > "System Configuration" > "Plugins".
- Search for "Sec1 Security Scanner" under "Available plugins".
- Install the plugin.
By default, Sec1 uses the following endpoints:
- API endpoint:
https://api.sec1.io - Dashboard endpoint:
https://unified.sec1.io
It is possible to configure custom endpoints by setting environment variables:
- Go to "Manage Jenkins" > "System Configuration" -> "System"
- Under "Global properties" check the "Environment variables" option
- Click "Add"
- Set
SEC1_INSTANCE_URLto override the API endpoint - Set
SEC1_DASHBOARD_URLto override the dashboard endpoint (used for report URLs in build output)
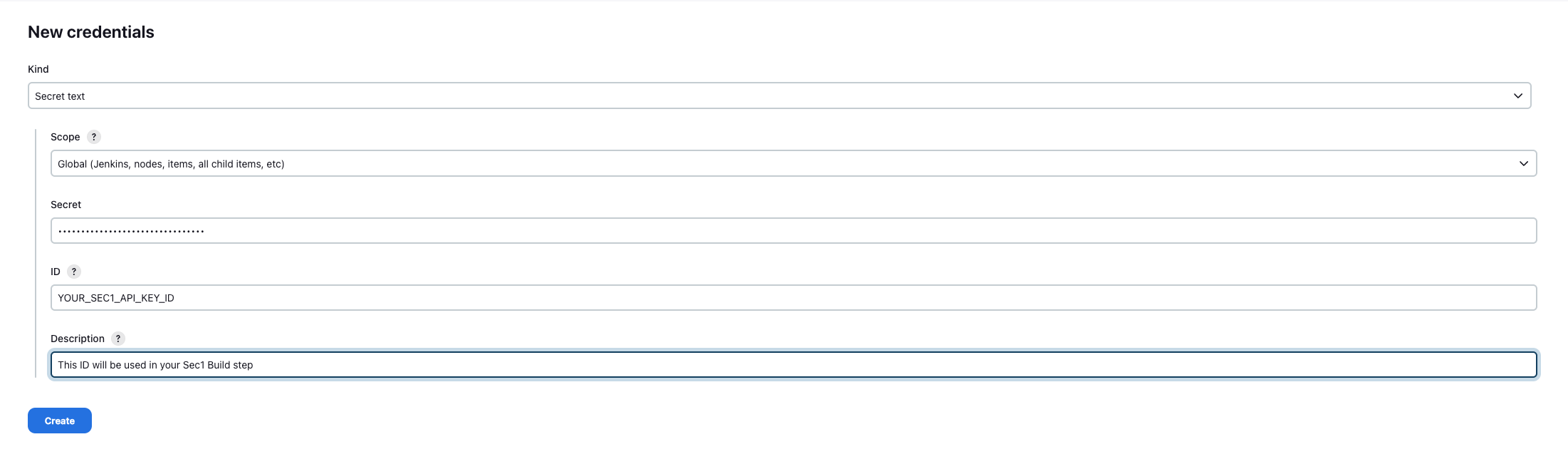
- Go to "Manage Jenkins" > "Security" > "Credentials"
- Choose a Store
- Choose a Domain
- Go to "Add Credentials"
- Select "Secret text"
- Add
<YOUR_SEC1_API_KEY_ID>as ID and Configure the Credentials. - Remember the "ID" as you'll need it when configuring the build step.
To get Sec1 Api Key navigate to My Account > "Login with GitHub" > Click on profile icon at top right > "Settings"
- In "API key" section, click on "Generate API key"
- Copy key for use.
This step will depend on if you're using Freestyle Projects or Pipeline Projects.
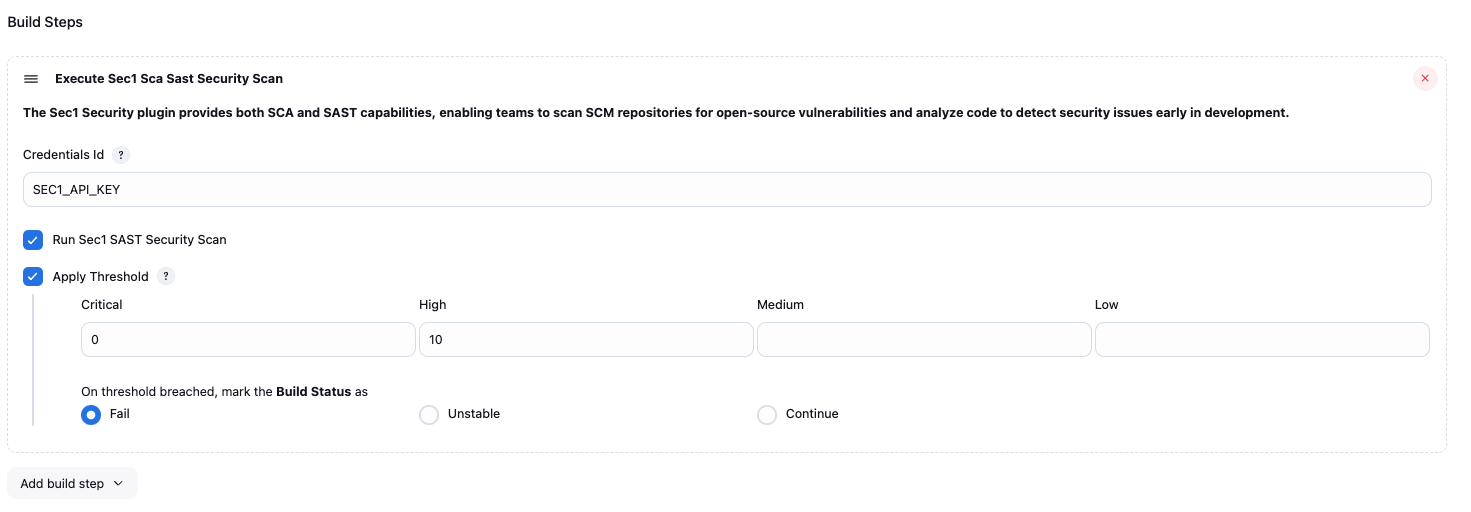
- Select a project
- Go to "Configure"
- Under "Build", select "Add build step" select "Execute Sec1 Security Scanner"
- Configure as needed. Click the "?" icons for more information about each option.
Use the sec1Security step as part of your pipeline script. You can use the "Snippet Generator" to generate the code from a web form and copy it into your pipeline.
You can pass the following parameters to your `sec1Security` step.📷 Show Example
pipeline { agent any stages { stage('Build') { steps { echo 'Building...' } } stage('Sec1 Security Scan') { steps { script { sec1Security( apiCredentialsId: '<Your Sec1 Api Key ID>', scmUrl: 'https://github.com/your-org/your-repo', runSca: true, runSast: true, scanTag: 'my-scan-tag', applyThreshold: true, actionOnThresholdBreached: 'unstable', threshold: [criticalThreshold: '0', highThreshold: '0', mediumThreshold: '0', lowThreshold: '0'] ) } } } stage('Deploy') { steps { echo 'Deploying...' } } } }
Sec1 API Key Credential ID. As configured in "2. Configure a Sec1 API Token Credential".
Git repository URL to scan. If not provided, the plugin attempts to detect it from the workspace .git/config or the GIT_URL environment variable. Use this parameter when auto-detection fails (e.g., on some pipeline configurations).
Whether SCA (Software Composition Analysis) scan needs to be executed for the configured git repository.
Whether SAST (Static Application Security Testing) scan needs to be executed for the configured git repository.
A tag to identify this scan. If not provided, the branch name is used. If the branch name is also unavailable, defaults to default.
Whether vulnerability threshold needs to be applied on the build.
Threshold values for each type of vulnerability. Example configuration: [criticalThreshold: '0', highThreshold: '10', mediumThreshold: '0', lowThreshold: '0']
If the scan reports more vulnerabilities than the configured threshold for the respective severity, an error will be shown in the console and the build status will be modified based on actionOnThresholdBreached.
The action to take on the build if a vulnerability threshold is breached. Possible values: fail, unstable, continue
To see more information on your steps:
- View the "Console Output" for a specific build.
-- Sec1 team